Ethernet Explained: Are Leased Lines Secure?
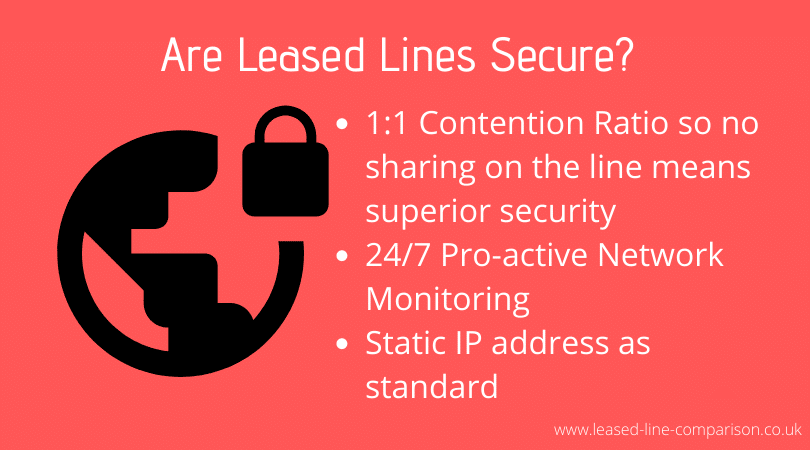
At a time when more and more businesses are becoming concerned about the risk of cyber attacks, one of the big questions on everyone’s lips today is ‘how secure are leased lines?’. The answer, of course, is very secure.
Ethernet Leased lines are also called ‘private’ lines, and they’re called that for a reason. Your provider, whether that’s BT or any other leased line provider, reserves that line exclusively for use by your company, which means that there is never any public traffic on your line, reducing vulnerability. Security measures will also be included in your service level agreement.
They will often come with static IP address as standard, compared to business broadband options which all use dynamic IP. Static IP addresses allow you to do things like run your own network on the line, but more importantly, they make your connection more stable.
There are also firewalls and specialist routers that can be added to a Leased line package to add to security. These will vary from provider to provider, so you’d need to do your research to find the best fit for your business.
Addressing the Risks
However, although leased lines are safe and secure, it is important for businesses to understand that there are still a number of risks, however unlikely they may be to occur. Some of these risks include:
● Accidental line cutting due to manual work (eg. street excavations)
● Intentional line cutting by a hacker
● Physical wiretapping, connecting to your company’s dedicated line
Although very rare, it is recommended that businesses draw up a contingency plan for unexpected situations, and take measures to ensure that their leased line remains as secure as possible.
Leased Line providers can offer back up lines. Some companies, who’s Internet connection is mission critical, will even pay for a second leased line for resiliency. This is not needed by most of us and tends to be for huge corporations who are targets of hackers worldwide, like google for example.
Keeping Your Leased Line Secure
The good news is your leased lines are already protected and the network is monitored 24/7 so any attempts at hacking are noticed.
There are a number of ways that businesses can help to protect their data and minimise the risk of confidentiality breaches should a leased line connection become damaged and vulnerable.
● Never rely solely upon the use of a leased line for data access. It is advised to always store essential information in the cloud which can be accessed from alternative locations.
● Encrypt very confidential data using a corporate VPN (Virtual Private Network). Should a vulnerability open your leased line up, the information that could be taken would prove not to be beneficial to hackers.
● If downtime is a major concern for your business, consider having a backup connection available, ideally from a separate carrier to maximise the chances of solid, continuous up-time.
The chances are extremely slim, so keep perspective.
Attacks on leased lines are very uncommon, and these dedicated connections are proving to be one of the most effective and efficient ways to boost security and minimise the risk of data exposure. Hacking a leased line is much more risky than hacking a business broadband connection, especially wiretapping which requires someone to be in the physical location of your offices.
You are much more likely to have your data compromised by an employee unwittingly opening a phishing e-mail or contracting a malware virus. Employee errors are the most common method of having your data hacked so education and training are key to reducing the chances of being hacked or getting a virus.
What to do if you have a security breach.
As mentioned above, attacks on leased lines are very rare, but there still should be precautions in place in case the worse happens. For now, we will focus on one type of security breach, a data breach. This is when data is intercepted by a hacker, this could be confidential files or customer records.
- Firstly, you need to identify where the breach is and stop it. This can be done by isolating the account that was hacked or isolating the part of the system that was hacked. This is important to stop the spread of the breach.
- Secondly, you must assess what data has been stolen, and what impact this could have on your business. For example, if they have taken customer data, this could be fatal for your reputation.
- Thirdly, warn those affected, for example, your customers. If your customer data was taken it is your duty to inform each customer whos data could be compromised.
- Lastly, learn from what happened and put preventions in place to stop this happening again. One way to do this is to run a cybersecurity audit to see what the weakness in your network is. Once you’ve figure this out you can correct them to make sure another breach doesn’t devastate your business.
Advice for Business Broadband Users
While there are now a number of insurance products designed to provide financial assistance in light of a cyber attack, this is more of a treatment than a prevention.
The best prevention investment you could make to help keep your business data secure is by simply upskilling & training your staff. Most business hacks and losses of data are because of human error so if you can help prevent the error you can maximise your chances of keeping your companies information secure.
If you are concerned about your data, then it is advised that you look into upgrading to a leased line, which is much more secure and can help prevent an attack from occurring, not just help you to recover from an attack. Leased lines are much more cost-effective than they were a few years ago, and you can now find great deals.
James Ward is CEO & Founder of Leased Line Comparison, a website founded in 2013 and has since helped over 10,000 customers. James gained his expertise in the leased line world by joining a telecoms company called Exponential-e back in 2011 which taught him everything he needed to know to set up this website today. James’ interests include horse racing, skiing, rugby, hiking, boxing and riding. He spends his time between family and friend, socialising and sport.
